As Supply Chain resilience and risks take center stage, Morpheus.Network, a SaaS middleware platform that provides exporters with a safe and secure Digital Footprint and Hanhaa, an IoT innovator with an intelligent cargo tracking and monitoring device, have once again developed a unique solution to implement the new USMCA rules for cross border shipments travelling from Mexico to the USA.
While medical supplies are rightly being prioritized, agro industrial products are following closely behind. Using a shipment of premium drinks as a case study, Hanhaa and Morpheus.Network will help companies understand the opportunities for trade, the political and economic climate and compliance challenges such as security.
Everybody Loves a Tequila
The rhetoric of recent years has led to escalating tariffs on imports from Mexico and has focused on forcing action on illegal immigration and drug trafficking.
The United States imported more than $345 billion in goods from Mexico last year, and shipped $265 billion south. There is a tight relationship in the supply chain whereby 30 percent of the content of Mexican exports, “La Maquilla”, originated in the United States, according to a recent study.
The United States imported nearly $28 billion in food and drink from Mexico last year, including more than two-fifths of its total imports of fruit, vegetables and 204 million litres of tequila worth $1.4 billion.
Have your Guacamole and Eat It. Trade and Security = C-TPAT
The dual threats of terrorism and smuggling require knowing the provenance, custody of ownership and the companies or persons handling goods during every step of the shipment. (C-TPAT) is a voluntary supply-chain security program led by Customs and Border Protection (CBP). Using approved technology and a focus on processes and risk analysis, a shipper, carrier and customs broker can ensure compliance without requiring large investments into IT infrastructure or resources.
A Quick Primer on C-TPAT
While most C-TPAT members typically focus on Section 4. cyber security policies, such as intrusion threats and disaster recovery, there are other areas equally important.
For Carriers and 3PLs, Section 5 on Asset states:
“Shippers work with their transportation partners to track goods from origin to final destination point. Shipment data, such as product ids, quantities, weights, and values, together with carrier assets such as VIN or Container IDs, and IoT track and trace must be consistent across all prevailing technology platforms. From ERPs such as SAP to CBP systems. This interoperability is managed using the Morpheus.Network middleware.”
Karl McDermott, Global Head of Business Development, Morpheus.Network
For Shippers, Section 7 for Procedural Security is key.
"We use our Secure Facility module to control all entry and exit points to inbond warehouses, maquillas and yards. Cargo that is stored temporarily must be secured. We solve this requirement using actionable triggers that detect motion using a geofence, or unauthorized access or tampering using light sensors."
Callum O’Hare, Head of Marketing, Hanhaa
When you couple the above challenges with unpredictable delays you wreak havoc on the tight lead times required by lean manufacturers or by the agro industrial vertical where farm to fork should be no longer than 5 days.
Smarter, Safer and More Secure USMCA Cross Border Supply Chains
With the smart integration of IoT and blockchain technology, supply chain and logistics managers have access to automated workflows that increase visibility and efficiency. This reduces supply chain operating costs such as delays, fines, SLA, rework, and reverse logistics.
Products are safer for consumers and buyers are protected from losses due to product deterioration, shrinkage, quality, IP theft and counterfeiting.
A Digital Footprint together with C-TPAT streamlines the release process, reduces CBP inspections, and priority processing for CBP with the end goal of creating secure shipments for cross-border trade.
As Supply Chain resilience and risks comes under new scrutiny, new USMCA rules will create a raft of opportunities. Customers using Morpheus.Network and Hanhaa can be pro trade AND pro security.
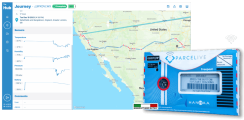
About Morpheus.Network
The Supply Chain SaaS middleware platform seamlessly integrating legacy and emerging technologies. Morpheus.Network provides shippers and exporters with a Digital Footprint for end to end shipment history that guarantees regulatory compliance and full load visibility for optimizing safe and secure supply chains saving time and money. https://morpheus.network/
About Hanhaa
ParceLive, is a real-time cargo tracking service that connects users to live information about the location, condition and security of their assets regardless of their country, carrier or scale.
ParceLive is being deployed internationally by leading logistics vendors and channel partners, and is now available directly to end-users wanting more control over the security of their assets.